Introduction
Before the advent of DevOps, most organizations performed their products’ security checks at the final stages of the software development life cycle (SDLC), irrespective of the development model adapted. Since the focus was predominantly on application development, security was deemed to be less important at other stages. Security checks are performed very late in the development cycle. Often, the product would be almost fully developed. Hence, discovering a security threat at such a late stage meant a lot of rework leading to waste of resources.
DevSecOps reduces the costs of fixing the security flaws by incorporating security into every stage of the development lifecycle, from the requirement stage to the operations stage.
Implementing DevOps results in better collaboration between teams, faster time to market, improved overall productivity, which enhances customer satisfaction.
DevSecOps emphasizes everyone’s role in security. It injects security practices into an organization’s DevOps framework. The goal is to incorporate security into all stages of the software development workflow instead of leaving it to the final stages of the SDLC.
DevSecOps do not replace your development model like Agile, rather complements it. Instead, they complement each other to help the organization maximize its benefits. Agile fosters collaboration and constant feedback. Unlike Agile, DevSecOps encompasses the complete lifecycle of a software product till production. DevSecOps provides methodologies and tools to facilitate agile adjustments.
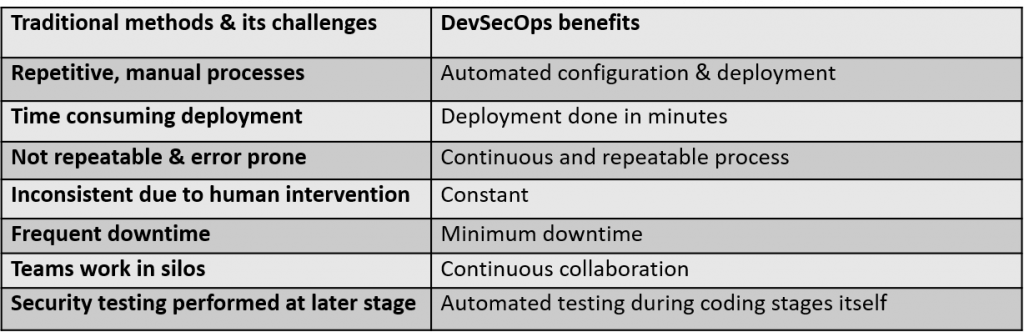
The value proposition of DevSecOps:
DevSecOps is the way forward for secure & efficient development as it improves the work culture & practices by bringing in automation across stages.
Implementing DevSecOps
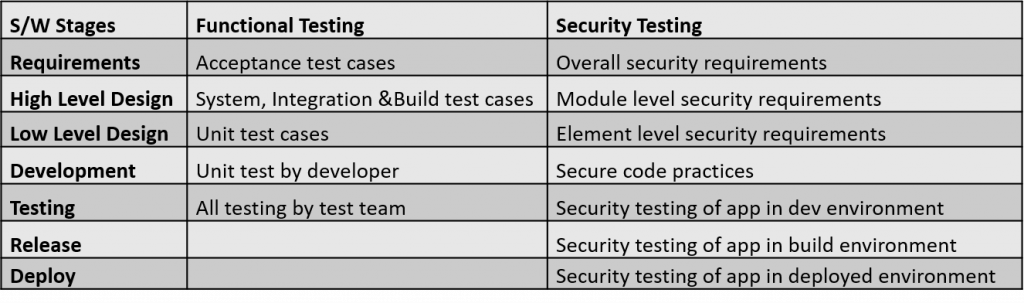
‘Security’ as culture starts from the initial stages of the Software Lifecycle and runs in parallel till deployment. The following table illustrates the lifecycle stages and compares the activities of functional & security testing teams.
Planning and Development
It all starts with planning. The acceptance test criteria, user designs, and threat models should be clearly defined.
Development being the next important stage, the teams should evaluate the maturity of their existing practices. The team should establish a code-review system that leads to a standard.
Building and Testing
Then comes building, where automated build tools do the tasks by converting the source code into machine code, using a build script. Automation tools come with a variety of powerful features. The tools can automatically detect any vulnerable libraries and replace them with new ones.
The next stage is testing, wherein the automated testing framework inculcates strong testing practices to the pipeline.
Deployment and Operation
Deployment is usually carried out through tools, as they automate the process and accelerate the pace of software delivery.
Operation is another crucial step, and periodic maintenance is a regular function to keep zero-day exploits at bay. DevSecOps utilizes tools to secure the organization’s infrastructure efficiently & eliminate human errors.
Monitoring and Scaling
DevSecOps uses powerful, continuous monitoring tools to ensure optimum performance of security systems.
Scaling also plays a vital role. Virtualization enables organizations to maintain large data centers, which are scalable.
Those are the basics in DevSecOps implementation. The DevSecOps roadmap could include additional steps depending on the size and complexity of the work.
DevSecOps Challenges
Of course, software implementation comes with a string of challenges irrespective of the model adopted. DevSecOps comes with its own set of challenges as briefed below:
Cultural Challenges
The biggest speed bump that discourages most organizations from moving to the DevSecOps approach is the reluctance of stakeholders. Not many will welcome a change to something they’ve been doing the traditional way. And the fact that security was considered more of an afterthought in the predecessor software development models doesn’t help either.
The traditional differing perception of the teams involved results in them working in silos. DevSecOps fosters an environment of collaboration by bringing developers and security professionals together. Another common belief is that increased security slows things down. To meet the demands of modern-day businesses, developers want to deliver their code rapidly.
The primary focus of security teams is to ensure the code is secure and for developers, to deliver on time. Since the objectives of both developers and security professionals do not meet, they find it hard to work in unison.
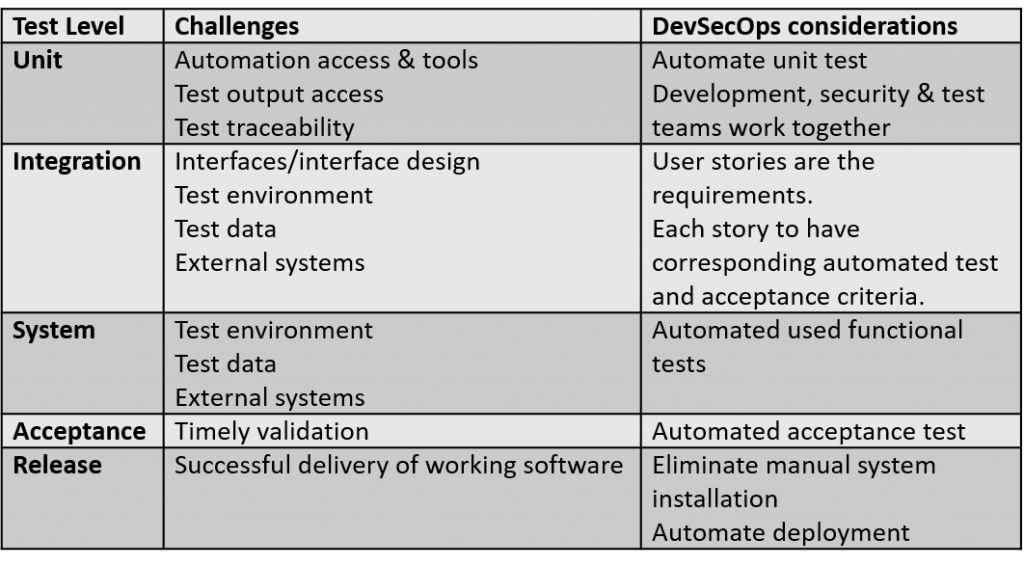
he following table presents test event-level challenges and DevSecOps considerations to overcome the same:
DevSecOps Benefits
Efficiency & cost reduction is achieved by detecting and fixing security issues during the development phases which also increases the speed of delivery. Bad publicity affects sales. One way of preventing that is to go in for proactive ‘threat hunting’.
Continuous enhancement is achieved by auditing, monitoring and establishing an effective notification system. By automating security review of code & testing, DevSecOps ensures the ‘secure by design’ principle. It also helps developers to use secure design patterns. Fosters a culture in which everyone takes responsibility for security besides a culture of openness & transparency.
DevSecOps Processes & Technical Considerations
DevSecOps pipeline adds two key concepts to the Agile development framework. They are
- Continuous Integration
- Continuous Delivery
Continuous Integration (CI) & Continuous Delivery (CD), often known as CI/CD, is achieved by systematically incorporating tools at all stages of SDLC.
Various aspects of Continuous Integration are:
- Source control
- Build
- Unit testing
- Packaging
- Source code repository
- Static code analysis
Various aspects of Continuous Delivery (CD) are:
- Configuration
- Integration & performance testing
- Production release
- Deployment
- Dynamic code analysis
Identifying the right tools for each of the aspects/workflow stages listed above is a critical step for successful & efficient adaptation of DevSecOps.
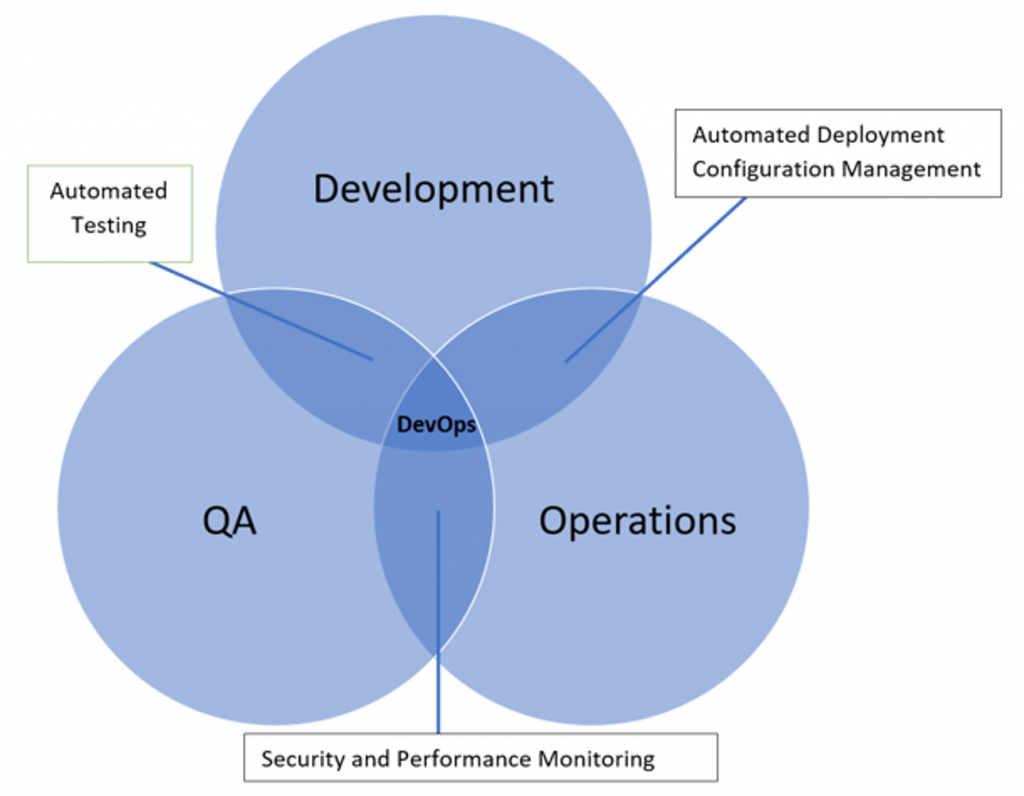
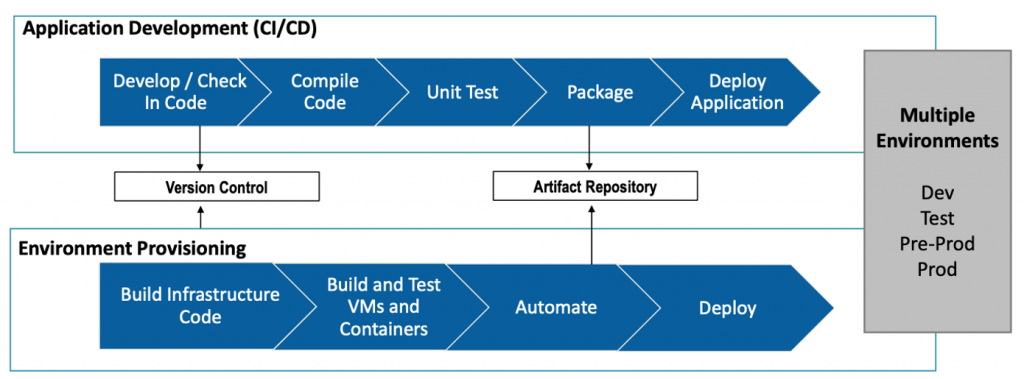
The diagram below explains how Dev and Ops are functioning in parallel in the development lifecycle.
Working in a Cloud environment brings its own risks & challenges. In DevSecOps, the security considerations needed to overcome the same are built-in.
Deployment Options:
In DevSecOps, the deployment can be done in two ways, either in Containers or Virtual Machines (VM)
- Containers:
- All applications share the OS and software bins/libs
- Containers are managed by the controller.
- Virtual Machine:
- Self-contained computing unit with host operating system
- Each application runs dedicated software binaries and a guest OS
- Managed by hypervisor
While each mode of deployment has its own advantages and disadvantages, from a security perspective, a Virtual Machine based approach offers mature procedures and tools.
Automation and Configuration Management
Leveraging the automation to implement DevSecOps is key to success. Automation makes auditing easier. Metadata, based on repeatable processes, makes decisions easier. Configuration management templates help to implement traceability of each code/configuration change, thus making it easier to identify deviations and the root cause of an issue.
Secure coding practices/Security as Code
Coding standards are regularly checked against new security recommendations. Similarly, all changes to the code are verified and tested against these recommendations. The benefits associated with such practices should be understood
Host Hardening
Host hardening is not a new practice. If used often, fewer services and applications would get exposed to the Internet. Lots of security incidents are directly related to leaving a generic attack surface, which allows automated attack tools to succeed. The hardening checklist and methodologies reduce the attack surface.
CI/CD for Patching
Once the metadata is created for each asset, it can be used to implement patching at the CI/CD level. Threat intelligence and Vulnerability Management feeds are compared to the deployed software stack. It helps to identify matches in the templates. It completely eliminates the patching of live systems. This provides an ability to have a risk exposure in near real-time.
Application-level Auditing and Scanning
Auditing and scanning are crucial to understanding the risk posture. Given below are few solutions for better security assurance of the code, as reflected in the organization’s risk appetite:
Source Code Scanning
Static Application Security Testing (SAST) can be implemented for scanning the source code. SAST identifies vulnerabilities and performs software composition analysis. It can be easily integrated into existing CI/CD processes. Implementing SAST tool enables remediation of vulnerabilities earlier in the software development lifecycle thereby reducing application risk and exposure.
Dynamic Application Scanning Tool (DAST)
Dynamic Application Scanning Tools scan the staging and production website in running state. It analyzes input fields, forms, and numerous aspects of the web application against vulnerabilities.
IDE Integration
IDE integration and static code analysis provide an enhanced view of the problems in the code. This is an effective way to optimize and mitigate vulnerabilities without having to leave the development environment.
Binary Scanning
All binaries are scanned for security issues derived from the coding checklist before they are digitally signed. The digital signature is treated just as the metadata itself. Within the CI, only signed binaries are implemented. This ensures the correct level of security sign-off.
Pre-Deployment Auditing
A pre-defined template for building assets ensures the desired security level. However, this should be supplemented by host-based scans. Security scanners do provide a compliance module, which allows importing templates.
Post-Deployment Auditing
Predefined templates once instantiated, can be checked for any delta against the pre-deployment scans to identify potential threats. API integration helps in achieving this.
Automated Vulnerability Management Scanning
All vulnerability management software should be integrated via API for infrastructure and web application scanning.
The real-time correlation of active threats against identified vulnerabilities leads to the identification of the following:
- Assets affected by known exploits
- New threats that may pose a risk to the business
The vulnerability management processes should ideally be integrated with any of the bug-tracking systems.
Conclusion:
In recent years, DevSecOps is widely discussed in developing secure software. There are many activities and practices are proposed to achieve the security goals of the enterprise. We believe an integrated security testing framework for a secure software development life cycle is essential.
We adopt the security activities and practices of DevSecOps to generate security guidelines and security test cases. Security testing tools are integrated to execute test cases automatically with our proposed framework.